NIST ISO/IEC 30107 Standard
There are two major certifications for face liveness detection and facial antispoofing, introduced since 2017. Both certifications — constituted by FIDO and ISO — are valid on par. FIDO also incorporates some clauses and rules from the ISO face antispoofing standard. Both certifications are considered legitimate for corporate certification and facial antispoofing certification.
The ISO/IEC 30107 face antispoofing liveness certification standard was introduced in 2017 in an effort to formulate and establish a clear picture of Presentation Attacks (PA) that are used against biometric and liveness detection systems including facial recognition and fingerprint scanning etc. The standard was developed by International Organization for Standardization in unison with the International Electrotechnical Commission.
To provide a more accurate selection of terms and definitions, the face antispoofing ISO/IEC 30107 standard also utilizes some other standards accepted by ISO, such as Biometric performance testing and reporting. The document lists attack types and their components, evaluation elements, and PA detection mechanisms. It also presents error rates, defines terminology and focuses on other related technicalities.

Levels of attacks
According to the face antispoofing ISO/IEC 30107 standard, there are 3 levels of a Presentation Attack Detection. The levels may vary based on: time, equipment, and the skill level of attackers.

Level 1. A level 1 attack has an average preparation time of up to 8 hours. The equipment required for such an attack is easily obtainable. It includes printed photos, dusted fingerprints, video of a target replayed from a phone, and palm photo etc.
Level 2. A level 2 attack has greater complexity and takes malicious actors up to 3 days of preparation. The tools for such an attack can still can be procured, but may require greater cost and effort. The attack is initiated by means of fingerprint casting, 2D or 3D paper masks, and face demonstration with eye movements etc.
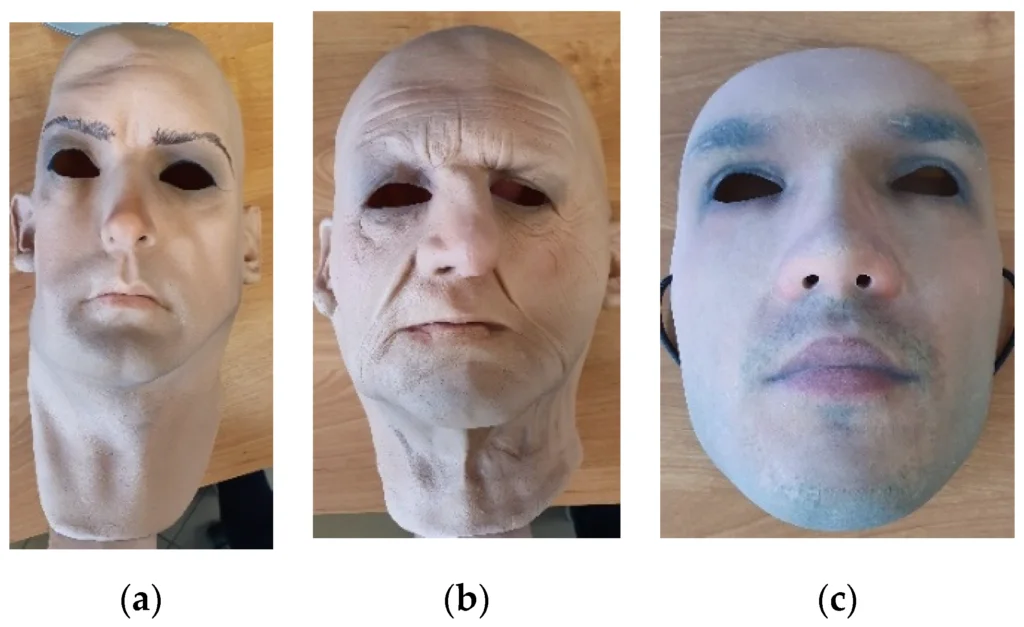
Level 3. A level 3 attack requires a preparation time ranging from 10 days to 3 weeks or more. Attackers need specified and rare skills for this level of attack and require professional equipment which is hard to obtain. To launch an attack, elaborate silicone masks with realistic face imitation are required.
Certification methodology
As observed by the facial liveness Wiki, the liveness certification process for the face antispoofing ISO/IEC 30107 standard is overseen by the iBETA laboratory. It offers a Quality Management System and biometrics test procedures and is accredited by NVLAP and FIDO Alliance.
The methodology includes:
- Presentation Attack Detection in accordance with the ISO 30107-3 standard.
- Spoofing and liveness detection.
- Enrollment attack detection, which involves a test attack simulated with a false human-imitating mask.
- Application evaluation, in which attack types are selected depending on application and use location/ environment of a system. This includes voice imitation with sound artifacts, facial recognition in a poorly lit room, and other examples.
- Biometric Performance Testing as dictated by ISO 19795.
- Biometric data subject collection. (This is considered a controversial matter from legal point of view, as collecting data from random people will likely be prohibited in the future).
Similar to the classification for attack types, the people being identified by the biometric system can also be grouped.
Certified vendors
There are a number of vendors who are accredited by the ISO’s facial anti-spoofing certification and its face antispoofing guidelines. A List of vendors certified with the highest level 2 (facial liveness only) is shown in the following table. The vendors are categorized by name, FNMR/BPCER limit, Passive/Active, and number of OS supported at certification:
| Vendor | FNMR or BPCER limit | Active or Passive | Hardware | Notes |
|---|---|---|---|---|
| Aware | 15% | Passive | iPhone 8 (iOS 13.6), Galaxy S8 (Android 8.0.0) | |
| ID R&D | 15% | Passive | Samsung Galaxy S8 Plus (Android 8.0.0), iPhone 6S Plus (iOS 12.1.4) | |
| Imageware | 15% | Passive | Galaxy S20 (Android 10.0.0), iPhone XR (iOS 12.3.1) | |
| Innovatrics | 15% | Passive | Google Pixel 2 (Android 8.1.0), iPhone 10 (iOS 14.2) | |
| Idemia (Passive) | 20% | Passive | iPhone 8 (iOS 12.1.4) | |
| IDMission | 20% | Passive | Google Pixel (Android 10) | |
| NEC Japan | 15% | Active | iPhone XR (iOS 12.3.1), Galaxy S20 (Android 10) | |
| Idemia (Active) | 20% | Active | iPhone 8 (iOS 12.1.4) | |
| OCR Labs | None | Active | Google Pixel 2 (Android 8.1.0), iPhone XR (iOS 12.3.1) | |
| Zoloz | None | Active | iPhone 7 Plus (iOS 13.3.1), iPhone 8 (iOS 13.3.1) | |
| FaceTec | None | Active | Samsung Galaxy Note 5 (Android, Version 7) | |
| EyeVerify | 15% | ? | iPhone 11 (iOS 14.4), iPhone 12 Pro Max (iOS 14.2.1) | |
| NEC Asia Pacific | 15% | ? | iPhone 12 Pro Max | Requires facial recognition for liveness check |
| iProov | 20% | ? | iPhone 11 (iOS 13.0) |
The complete list of certified enterprises can be found on the iBETA website.
FIDO Certification
In October 2020, FIDO (Fast Identity Online) published a comprehensive report on assessment methods, attack types and terminologies used for testing a biometric system. This face antispoofing test measures data related to Failure-to-Enroll Rate (FTE), Impostor Attack Presentation Accept Rate (IAPAR), Failure-to-Acquire Rate (FTA), and Zero-Effort Impostor Attempt etc.
The system under test is dubbed Target of Evaluation (TOE) and its components — data capture, signal processing, comparison-and-decision — are subjected to simulated attacks. The standard requires that the Target of Evaluation be placed in a test environment, which simulates the actual "field" environment where the system is going to be installed. For instance, it implies noisy surroundings for voice identification or premises with dim lighting for facial recognition. If a TOE is designed to work in varying environments, each must be simulated separately to meticulously test the face antispoofing capability.
Levels of attacks
FIDO categorizes presentation attacks in three levels which are differentiated by the time, effort, and resources required to orchestrate them. The complexity of equipment required also grows as the levels progress.
The levels defined by FIDO are:
Level A. This level includes the most primitive and crude, yet sometimes effective attack methods. Among them are photo print-outs, including those made from high-definition originals, as well as the target’s images presented on a phone/tablet screen.
Level B. This level involves more evolved impostor techniques including the use of masks, which vary in quality — from simple and cheap 2D masks to intricate and more creative versions made using a 3D printer. Videos picturing a target are also used.
Level C. In this level, malicious actors employ artfully designed, realistic silicone masks or high-definition videos, including deepfakes, to trick the face antispoofing system. The masks can also be designed to emit artificial warmth to simulate a more realistic human face.
Certification methodology
The certification for face antispoofing testing is performed by FIDO-accredited independent testing laboratories on products or systems provided by vendors. The evaluation measures the Impostor Attack Presentation Match Rate (IAPMR), as defined in ISO 30107 Part 3.
The certification procedure includes:
- Presentation Attack Instruments (PAI). These are tools — masks, printouts, mobile phone videos — that should be used during a test.
- Test Crew. It is required that at least 10 people, who will play the role of subjects examined by the biometric system, must participate in the test. Their biological organs — eyes, fingers, etc. — used for the test are referred to as "unique samples".
- Time. Each level has a defined time for attack attempts: Level A - up to 1 day, Level B - up to 7 days, Level C - 7 days.
When the metadata based on above mentioned areas is gathered, a detailed report is submitted to FIDO. Testing is conducted by one of the FIDO Accredited Biometric Laboratories who focus on face antispoofing among all else (see the table below)
Difference between ISO/IEC 30107 and FIDO
Both ISO/IEC 30107 and FIDO standards of face antispoofing are highly detailed when it comes to defining threats, testing systems and envisioning challenges. Additionally, the two standards are literally intertwined, as a FIDO certification accepts many of the terms proposed by ISO/IEC 30107 standard.
Both ISO/IEC 30107 and FIDO pursue the same goals of revealing vulnerabilities of biometrics systems, perfecting their performance and classifying problems and threats. Major discrepancies lie in the terminology used by both face antispoofing standards and slightly different attack types proposed by them.
| Species | ISO/IEC 30107 Level | FIDO Level |
|---|---|---|
| Face image printed on inkjet or laser printer | 1 | А |
| Face image printed at photograph laboratory | 1 | А |
| Displayed photos on electronic/mobile devices | 1 | А |
| Displayed videos on electronic/mobile devices | 1 | В |
| Paper masks | 2 | В |
| Masks made of specialized materials (ceramic, silicone, and/or theatrical) | 3 | С |
| 3D printed faces | 3 | С |
References
- SO/IEC 30107-1:2016 standard
- ISO official website
- IEC official website
- ISO/IEC 19795 Biometric Performance Testing and Reporting
- iBETA Laboratory official website
- National Voluntary Laboratory Accreditation Program (NVLAP)
- ISO/IEC 19795-1:2021
- Biometric data and privacy laws (GDPR, CCPA/CPRA)
- Towards the Security Evaluation of Biometric Authentication Systems
- FIDO Biometrics Requirements
- FIDO Announces Latest Set of FIDO Certified Products
- Innovatrics DOT Passive Liveness Application - V2.1.0(1) iOS/V3.0.0 Android PAD Level 1 Test Report








 Antispoofing
Antispoofing



