General Overview
Essentially, biometric spoofing combines two elements: 1) Production, and 2) Presentation. The production stage involves creation of a synthetic artifact that imitates a certain biometric trait such as a voice, a face, a fingerprint, an eye retina, etc. The presentation stage is when that artifact is presented to the sensors of a biometric system with the goal of bypassing it.

The word “spoof” traces back to a late 1800s card game involving deception. In the context of information security, the term was initially used in 1989 when the computer engineer Steven Bellovin first addressed the issue of IP spoofing. One year prior to that, another researcher Robert Morris designed the famous Morris worm — a malware that could execute an IP spoofing attack.
It is suggested that spoofing attacks appeared together with the first biometric systems — such as the earliest commercial hand geometry recognition developed at the University of Georgia in 1974.
A perfect example of involuntary spoofing happened back in 2001 at the Tampa Super Bowl, when fans were unaware that they were guinea pigs for a new facial recognition software. Though never proven, Tampa police claimed they identified 19 suspects in the crowd with valid arrest warrants thanks to the facial scans.

The threat of spoofing began to receive serious attention in 1998 when, presumably, the first instance of fingerprint spoofing was reported by NETWORK computing. The first liveness detection competition, LivDet, began in 2009 — sparking a constellation of other biometric challenges seeking to discover the best antispoofing technology.
Spoofing Evaluation
In order to combat spoofing, we need to evaluate its components so that proper benchmarks can be set:
Datasets
Public and standardized datasets allow impartial and reproducible evaluation of different aspects of biometric security. As mentioned, researchers and institutions at times ignore the legalities; however, datasets should be legally compliant to avoid privacy violation and distribution issues, which may spark ethical controversy. Datasets should be statistically meaningful, meaning they have an adequate proportion of real/fake samples and minimization of gender and racial bias.

Dataset content should feature various acquisition methods, artifacts such as noises or inconsistent illumination, and other elements that diversify the attack data. This measure will help to mitigate laboratory vs. real life and prepare a system for unconstrained conditions.
Algorithm and system approaches
Algorithm-based evaluation allows attesting the liveness detection software side of the solution and its various techniques. The chief advantage of algorithm-based evaluation is that it is universal for current solutions. This means a large number of liveness detectors can be appraised with the same datasets and protocols.

System-based approaches target the hardware of a detection system and do not provide the same evaluation flexibility as algorithm-based methods because the hardware architecture (including sensors) is unique in each case. Despite this drawback, system-based approaches are useful because they allow for examining it's commercial efficacy in real life.
Main Types of Spoofing
In liveness taxonomy, spoofing types and techniques are predetermined by the existing biometric modalities, among which fingerprint, face, and voice recognition are the most prevalent. Other modalities are also spoofed, though to a lesser extent. The following types are classified by the facial Antispoofing Wiki:
Facial Spoofing
Facial authorization is the world’s second most popular biometric modality. Moreover, facial images are a mandatory part of the identity documents throughout the world and there is an uptick in camera surveillance equipped with face recognition algorithms. For example, as of 2021, China alone had a staggering 540 million CCTV cameras installed.
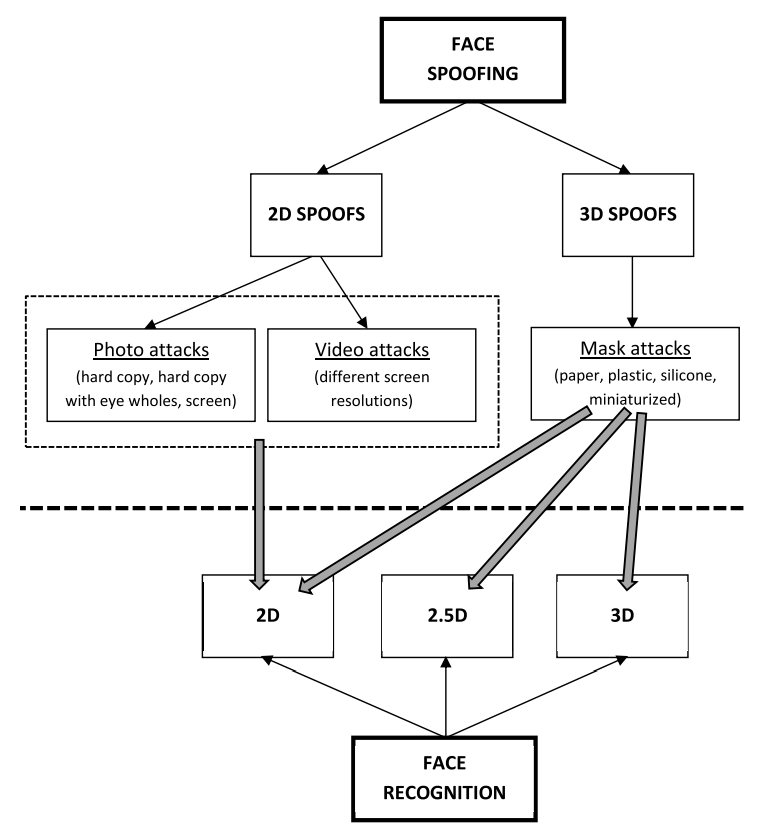
Malicious actors mostly resort to direct Presentation Attacks (PAs) to bypass facial authentication. Although indirect or injection video attacks are also observed by the research community.
PAs employ a repertoire of attack instruments (PAIs) that vary in quality and creativity. They range beyond simple facial cutouts to elaborate three-dimensional realistic masks made from latex to resemble human skin, deepfake manipulations, high-level makeup, and even plastic surgeries.

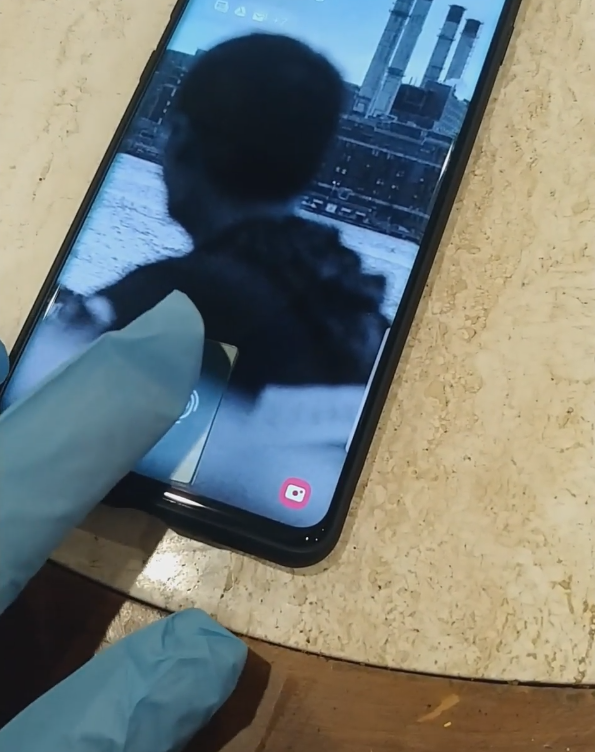
Injection attacks imply tampering or replacing video data received by the system with a fake video stream and then presenting it on an internal level — in this case, the system’s sensors are not physically enganged. To mitigate injection attacks, organizations should employ FIDO and ISO-certified anti-spoofing solutions: fingerprint scanners, facial liveness detectors based on thoroughly tested neural models, etc.
Voice Spoofing
As of 2020, about a half of all smartphone users used voice technology integrated into their devices. While this modality certainly decreases customer friction, it can also be vulnerable to speech synthesis, replay, voice conversion, and impersonation attacks.
Automated Speaker Verification (ASV) systems equipped with liveness detection can effectively fend off voice spoofs with such safeguards such as speaker identification and verification based on a biometric reference or simply prompting the user to say a pass-phrase. However, even the most sophisticated systems can be still vulnerable to a degree.
Voice cloning tools, which are freely available online, only aggravate the issue as their output offers a new level of realism. Speech synthesis, particularly based on the Hidden Markov Model, was first proved to be a threat in 1999. There is also the fact that the mobility of modern devices may lead to audio disruptions during a verification stage (such as in crowded spaces) or use of different microphones, which affect sound quality.
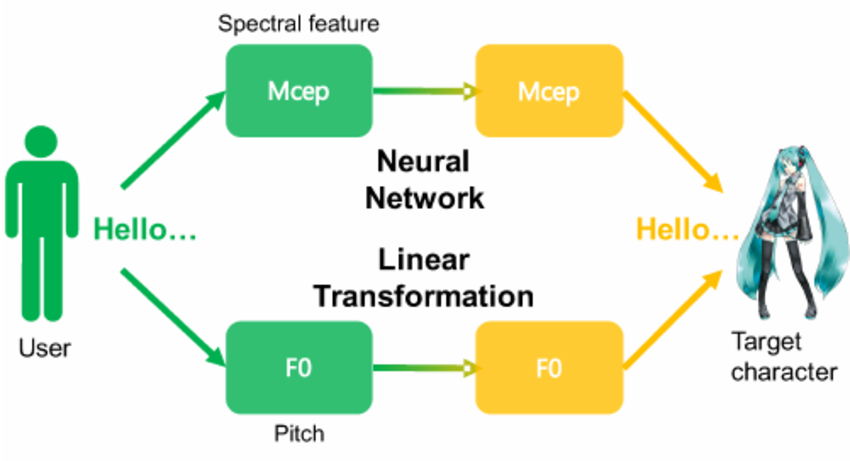
Currently, a diverse range of voice antispoofing methods can be used to protect against both replay and synthesis attacks — human impersonation is not considered a threat to ASV systems. They include phase spectrum analysis, F0 pattern examination with the unit selection approach, baseline EER monitoring for exposing voice conversion, and others.
Fingerprint Spoofing
Fingerprint recognition still remains the most popular biometric modality, even though the fingerprint sensor market is falling behind facial recognition in 2022: $4.85 billion vs. $5.48 billion.
Fingerprint recognition is based on analyzing basic patterns — whorls, loops and ridges — that are observed in human fingerprints. They are unique for every individual and do not change their structure over the time, with some slight exceptions. The main recognition algorithms are minutiae matching, correlation-based matching and non-minutiae feature-based matching.
Fingerprint PAIs are usually replicated with simple and available materials: clear gelatin, modelling clay, silicone, etc. Fingerprint samples can be procured through deception or coercion, as well as from leaked databases or even high-definition hand photos.
Iris Spoofing
The human iris is reported to be 5 times more unique than a fingerprint, which also suggests a higher accuracy. At the same time this modality is sensitive to at least two types of PAs: printed/replayed and prosthetic eye attacks.

The former type involves either printed copies or digital iris photos presented from a high-definition screen. The latter type is much harder to execute as it requires higher financial expense and skill level.
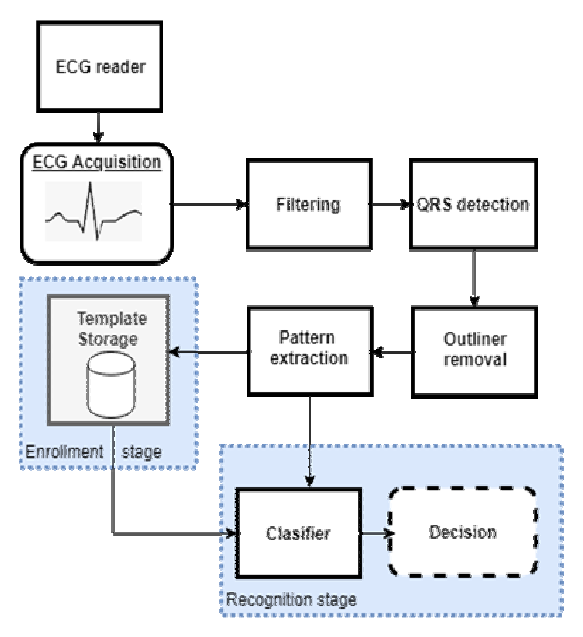
ECG Spoofing
Electrocardiogram recognition is reported to be high in uniqueness and performance and medium only in measurability. ECG signals are highly unique for every person, although they can be unstable and fuzzy in case of emotional stress or physical activity.
On the common user level, ECG signals are registered with either smartwatches or wrist identity wearables such as the Nymi Band. However, cases of successful ECG spoofing have been discovered. An experiment by Eberz et al. demonstrated that an ECG signal can be intercepted and used for attacking a wearable authentication device.
Spoofing in Multimodal Systems
Multimodal systems combine two or more biometric modalities: fingerprint + face, ECG + vein, and so on. They are generally believed to diminish success chances for spoofing as bypassing more than one modality can significantly increase the amount of cost and effort. However, a study by Rodriguez et al. suggests that bypassing one modality escalates the probability for spoofing others successfully.
Curious to learn more about multimodal liveness techniques? Read on here.
References
- Steven M. Bellovin was at the forefront of spoofing studies
- Studying The History Of Ip Spoofing Information Technology Essay
- Morris worm (Wikipedia)
- That Time the Super Bowl Secretly Used Facial Recognition Software on Fans
- Hand geometry recognition is considered the first commercial biometric system
- Liveness in biometrics: spoofing attacks and detection
- Large Crowdcollected Facial Anti-Spoofing Dataset
- Biometric Spoofing: A JRC Case Study in 3D Face Recognition
- Facial recognition system Vocord tested in ‘field’ conditions
- International Biometric Group Announces the Availability of the Biometrics Market and Industry Report 2009-2014
- Surveillance camera statistics: which cities have the most CCTV cameras?
- Biometric Antispoofing Methods: A Survey in Face Recognition
- The man in the latex mask: BLACK serial armed robber disguised himself as a WHITE man to rob betting shops
- Realistic latex masks are used for spoofing and identity concealment as in the ‘betting shop’ robberies incident
- Voice Search Statistics and Emerging Trends
- What is Customer Friction and How Do You Relieve It?
- On The Security Of Hmm-Based Speaker Verification Systems Against Imposture Using Synthetic Speech
- Schematic representation of voice conversion, which can be used for spoofing
- Spoofing and countermeasures for speaker verification: A survey
- F0 pattern examination
- Fingerprint Sensor Global Market Report 2022
- Facial Recognition Global Market Report 2022
- Fingerprints change over time, but not enough to foil forensics
- Reddit user
- I attempted to fool the new Samsung Galaxy S10's ultrasonic fingerprint scanner by using 3d printing
- German Defense Minister von der Leyen's fingerprint copied by Chaos Computer Club
- A high-quality ocular prosthesis with a realistically painted retina
- Broken Hearted: How To Attack ECG Biometrics
- A Review Of Ecg Based Biometric Systems
- A Survey on Antispoofing Schemes for Fingerprint Recognition Systems

 Antispoofing
Antispoofing



