Remote KYC: Basic Requirements
Remote KYC is based on creating a costumer’s profile to establish, verify and confirm their identity based on biometric standards, liveness taxonomy, etc. Requirements for this profile may vary for different companies/organizations. Typically, they include customer information such as:
- Age
- Name
- Address
- Identification number
- Bank and the account type
Additionally, they can include GPS location, tax status, professional occupation, shopping or money transaction patterns, size and reputation of the customer’s bank, preferred payment methods, and also anything pertaining to the liveness definition.
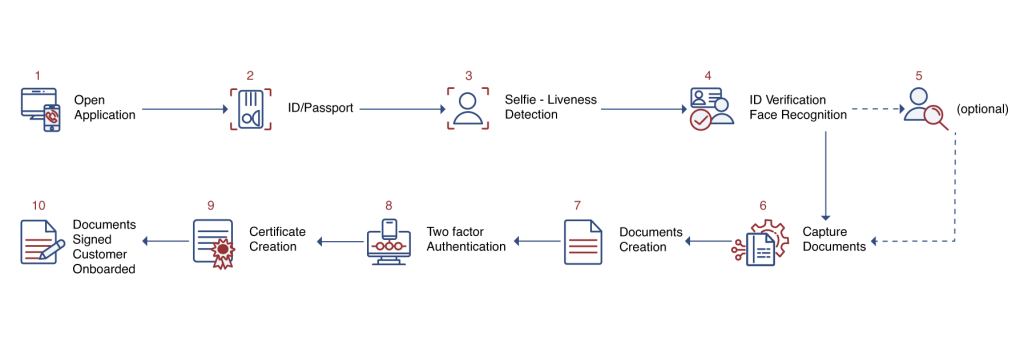
Remote KYC often only requires a regular smartphone to conduct customer verification — provided that the phone allows taking biometric data. The system is capable to conduct face recognition, create a unique person’s ID, provide two two-factor authentication (2FA), and apply further security measures if necessary. While these measures greatly increase security, they may be easily deceived in the absence of liveness detection.
Spoofing Attacks
Introduction
Liveness detection is a key element of the KYC system. As ID Watchdog reports, malicious actors often use profiles of deceased people for identity theft. This also creates a threat to their social media profiles. Liveness detection is also essential in preventing Presentation attacks (PAs). Fraudsters can use synthesized voice, video deepfakes, masks, fake fingerprints, and even sculpted heads to bypass recognition systems. These fraudulent methods can be detected using liveness detection.
Remote KYC works primarily on mobile gadgets. As statistics show, half of all shopping traffic in the world goes from the smartphones and tablets. A fingerprint scanner + phone camera tandem can be a powerful verification tool, especially when backed by a properly designed liveness recognition system. Spoofing attacks aimed against remote KYC can be separated into two categories:
Physical attacks
Physical attacks are pretty similar to the presentation attacks. A fraudster can employ a vast repertoire of tools:
- Mask. Similar to a presentation attack instrument (PAI), masks can drastically vary in quality and effectiveness. They range from commonly used simple 2D masks to more elaborate masks made from silicone that mimic skin texture.
- Replay attacks. Often targeting anti-spoofing for IoT, this attack involves use of a high-resolution screen, on which a target’s face is displayed. It can be a static image, pre-recorded video, or a deepfake.
- Photo. A simple printed photo is the cheapest PAI to produce. However, it is considered a rudimentary attack, as most modern smart gadgets can detect it. A 2019 experiment showed that nearly 60% phones out of a diverse sample size could detect when a fake printed photo was presented in place of a face.
- Fake ID. Buying a fake ID with a lookalike person has also been reported as a possible attacking technique. However, his technique is not common due to insufficient evidence.

Digital attacks
The purpose of a digital attack is to sabotage a smart gadget by hacking it. It can be done by installing a malware in the system to intercept or alter genuine input of the camera. Malicious actors also use sophisticated techniques — like portrait animation or face swap — to trick the system into believing they are the legitimate user. Digital attacks can sometimes even fool active detection where the system proposes a verification challenge — asking a person to blink an eye or smile to confirm their liveness. Perpetrators can achieve this with applications such as Face2Face.
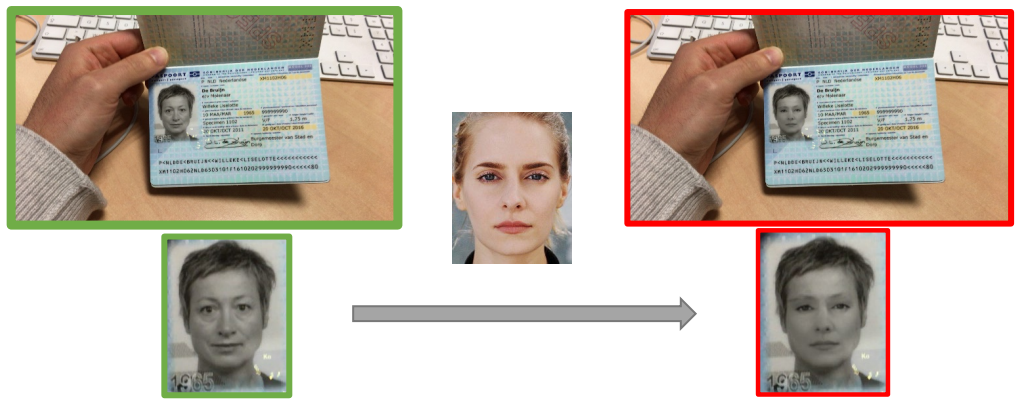
Face morphing is another malicious technique that poses a serious threat to face recognition systems. A morphed face is able to retain biometric features of multiple people. Therefore, a face recognition system can identify at least one of them successfully. As a result, a whole group of perpetrators can access a system. A similar technique can be implemented in real-time ID photo replacements (See this Antispoofing Wiki article for more info).
Both physical and digital attacks can jeopardize a KYC system, therefore, adequate countermeasures are important. Fortunately, there exist multiple technologies that can be used to counter these attacks.
Physical Attacks & Counter-Measures
When it comes to the presentation attacks, various methods have been proposed to increase the security of facial recognition systems.
Regulation measures
The European Union Agency for Cybersecurity (ENISA), offers a five-step algorithm that can ensure that a system is accessed only by a legitimate person:
- Initiation
- Attribute and evidence collection
- Attribute and evidence validation
- Binding and verification
- Issuing of Proof
This method requires the user to submit some components and conditions. They include a physical photo of a person, the NFC chip to provide confidence match, government-issued ID, and other elements.

Although cumbersome, these requirements are important for failproof security. The EU plans to allow citizens to access government resources digitally, and has therefore proposed these steps to ensure identity protection on all levels. As an extra security measure, the eiDAS regulation was suggested. It stands for Electronic Identification, Authentication and trust Services and implies that national electronic identification schemes (eIDs) will be used to prevent fraud.
Hardware solutions
Face unlock feature has been a source of controversy for many years now. In 2018, Kaspersky laboratory even called it a "bad idea" based on the low security measures and weak algorithms of most phones. However, modern phones models like Google Pixel 4 have made efforts to increase facial unlock security by employing 3D mapping of infrared dots. This helps to examine the skin texture of a presented face to reject a fake one. At the same time, some novel hardware solutions are also proposed. A special Trinamix camera can detect various materials: from metal to wood allowing it to successfully tell a silicone mask from a human face.
Software solutions
There is a broad array of methods used for detecting a presentation attack through software. They include capturing and analyzing the variations of local-binary pattern (LBP) descriptors, noise signature, and distortion artifacts etc. As a rule, software solutions require interference of a neutral network. A Convolutional Neural Network (CNN) can be used for the representation or feature learning method. In essence, the CNN will focus on learning intermediate representations by analyzing the pixel data input. For instance, local facial features can be extracted by the network to sculpt the so-called depth maps of a person’s face. Such a map can be used for detecting whether a presented object has a realistic depth of a typical human face or not.

Digital Attacks & Counter-Measures
Currently, there are not many techniques that can effectively combat digital attacks. The most reliable ways to avoid such attacks include using an antivirus app, avoiding suspicious corners of the web and keeping gadgets away from potential perpetrators. However, some alternative methods also exist. One of them is dubbed Portrait seal. It serves to prove an authenticity of an image. Among all else, it can be used to confirm that a presented ID is genuine. A CNN can help detect and prevent a digital attack, especially an identity swap. Such a face manipulation leaves certain artifacts, generated by a deepfake tool. A CNN-based system can extract features from the video data and spot these artifacts. However, digital attack mitigation still has along way to go and presents open questions for research, discussion and experimenting.
Liveness in the KYC Protocol: Meaning & Techniques
Know Your Client or KYC principles were first formulated in the early 1990s with countries like Luxembourg and Australia widely adopting them. In the late 2000s eCommerce saw rapid growth which also attracted increased attacks by fraudsters. As a response, numerous security measures were proposed. Online or remote KYC — sometimes referred to as eKYC — was one of them.
Today, remote KYC compliance is mandatory in almost all countries: 190 jurisdictions follow the Customer Identification Program (CIP) guidelines suggested by the FATF. KYC is used by the payment providers, mortgage companies, banks, brokerage firms, charities, and other institutions. Online sellers and businesses also greatly benefit from it: KYC helps to protect companies from false chargebacks, money laundering, identity theft, and other serious threats.
FAQ
What is KYC?
Know Your Customer (KYC) is an international security standard used in commerce and banking.
Know Your Customer (KYC) is a security standard introduced by FINRA in 2009. It helps in verification of a person intending to initiate a financial transaction such as opening an account with a bank, business or a commercial service that operates online or offline. The standard is adopted worldwide and is mandatory for payment processors: it helps to protect financial institutions and businesses against issues like false chargebacks, identity theft, credit card fraud, money laundering (to an extent) and terrorism financing etc. KYC also serves as a spoofing counter-measure. When used with digital platforms, (e)KYC employs a broad range of antispoofing tools in order to increase security of video, fingerprint, and voice identification processes.
What is AML?
Anti-money Laundering (AML) is an international security standard used in banking.
The Anti-money laundering standard (AML) has been in development since 1989, when Financial Action Task Force (FATF) was established. The standard seeks to prevent legalizing funds obtained through criminal schemes, as well as trading illegal items on black market, tax evasion, embezzlement, terrorism sponsoring, etc.
AML in tandem with KYC is adopted by banks and payment providers (like Amazon Pay) to maintain a secure environment. Biometric recognition and liveness detection play a significant role in AML. They help prove a presented user's identity and authenticity, therefore mitigating the risk of money laundering and fraud.
How does liveness work for KYC?
Liveness detection is pivotal in KYC as it helps to verify a person's authenticity.
Know Your Client (KYC) — is an international standard used in e-commerce, banking, and other commercial and non-profit areas. It helps to prevent false chargebacks, identity theft, authorized access, money laundering, and other types of fraud.
KYC employs tools such as liveness detection in order to identify whether a client is a real, authorized person or an imposter/fake identity using their credentials. In other words, Liveness detection guarantees that a person, who wants to execute a financial operation, is a legitimate and trustworthy client. The detection is carried out via ordinary smart device functions/applications such as mobile camera, fingerprint scanner, and a microphone as verification tools.
References
- As ID Watchdog reports
- Half of all shopping traffic in the world
- A 2019 experiment
- Buying a fake ID
- An example of a spoofing mask
- Face morphing-like technique applied to an ID
- Offers a five-step algorithm
- ENISA’s confirmation algorithm
- eiDAS regulation
- Why face unlock is a bad idea
- Trinamix camera
- Detecting face presentation attacks in mobile devices with a patch-based CNN and a sensor-aware loss function
- An attempt to unlock a phone equipped with a skin detector
- Portrait seal
- Widely adopting them
- Customer Identification Program (CIP) guidelines
- FATF

 Antispoofing
Antispoofing


