Problem Overview
Internet of Things or IoT is a technology that interconnects physical objects and systems by embedding sensors, software and data exchange capabilities in them. The first IoT device was introduced in the 1980s, when a group of students at Carnegie Melon University "taught" a Coca-Cola vending machine to send out a signal if it was out of soda cans. The term itself was coined in 1999 by Kevin Ashton — a pioneer RFID (Radio Frequency Identification) researcher.
IoT has a major application in smart home systems, whereby users can control different home functions like security, lighting, temperature etc. remotely using smart devices. In the early 2000s, smart home systems, based on IoT principles, were relatively unknown. They became a mainstream phenomenon after the release of Google Home in 2016, initiating the Internet of Things era. Smart hubs like Google Home or Amazon Echo were launched, and allowed users to access a multitude of domestic appliances remotely: lights, thermostats, surveillance cameras, sound systems, home security and so on.
It is estimated that by 2020, there were already 38 billion IoT devices in use around the world and the number is expected to grow to 83 billion by 2024. (By Juniper Research). Since IoT technology often makes use of biometric recognition for security and control of connected devices, it naturally attracted the attention of malicious actors who sought to use spoofing attacks to gain access to these devices. In turn, it gave a spark to the antispoofing for IoT development.

Threats Presented by the IoT Vulnerabilities
As mentioned by the facial antispoofing Wiki, Internet of Things allows users to control multiple gadgets through online and remote access. The key to this control is a regular smartphone. IoT devices as well as many apps designed for them contain a significant amount of sensitive user data, and are therefore, highly vulnerable to attacks. These vulnerabilities can be mitigated by hardware-related constrains, however, adding extra security components to smart control apps and systems would become expensive for an average user.
Hence, the threat to IoT security due to inherent weaknesses of the devices and systems, has persisted. For instance, in 2020 it was reported that IoT devices presented a major flaw, which made Bluetooth spoofing possible.

The security breach, dubbed BLE Spoofing Attacks flaw, was caused by the reconnection process. When user authorized Bluetooth devices drop out of the range of connected home devices, the connection is lost. Once they reappear, they get re-connected, without having to go through authorization again revealing a serious security gap.
Another serious threat was revealed in 2016: the Owlet Wi-Fi heart monitors proved to be hackable, bringing the company a "Worst IoT Security Of 2016" anti-award. Originally designed for alerting parents about abnormal heart activity of their child, Owlet proved to be highly vulnerable to outside threats. Adversaries could potentially forfeit the genuine data transmitted by the monitor, which could result in child deaths.
Another peculiar case was registered in 2015, when two researchers hijacked the control of a Jeep SUV while it was moving. They managed to activate the vehicle's windshield wipers, radio and even disrupt transmission, causing the vehicle to stop.
Attacks on SmartHome Platforms
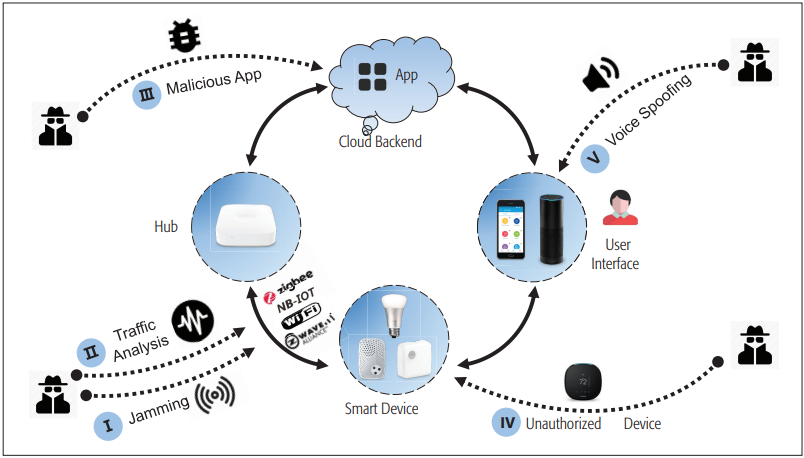
To understand how IoT attacks are executed, it is necessary to know the "anatomy" of the targeted systems. The main components of an IoT system as shown in our facial Antispoofing Wiki are:
- Smart gadget. This type of gadget is different from "traditional" appliances due its capability of network communication. More specifically, IoT devices employ wireless communication protocols: Bluetooth, Wi-Fi, and others that help them to connect to other devices.
- Hub. Hub is where the cloud back-end and wireless connection meet. It accepts data coming from the sensors, shares it with the cloud-powered back-end, and then returns commands if necessary. It plays the role of a "brain" in the system.
- Back-end. Stored on a cloud, the back-end delivers the control logic, instructing the smart gadgets on what commands to follow. Cloud technology has become integral in IoT systems to lower energy consumption.
- Interface. This component plays the role of the "remote control". In most cases, it’s a mobile application, through which a user can control their smart gadget. Voice commands have become especially popular in controlling smart systems lately, as the VUI technology (Voice User Interface) has become greatly accurate and user-friendly.

All four components of the IoT system have unique vulnerabilities that can be targeted in a security breach.
Researchers highlight 5 major attack types that target IoT systems:
Jamming Attacks
Listed in livenss taxonomy, a jamming attack targets the physical layer of a SmartHome system. In essence, it is quite simple: the attack generates disturbances, to disrupt or "jam" communication between the gadget and the hub. The disturbances are produced in the same frequency range that the smart system employs to let the gadgets "parlay" with each other. This can be done with a high-power radio source, which is quite easy to assemble.
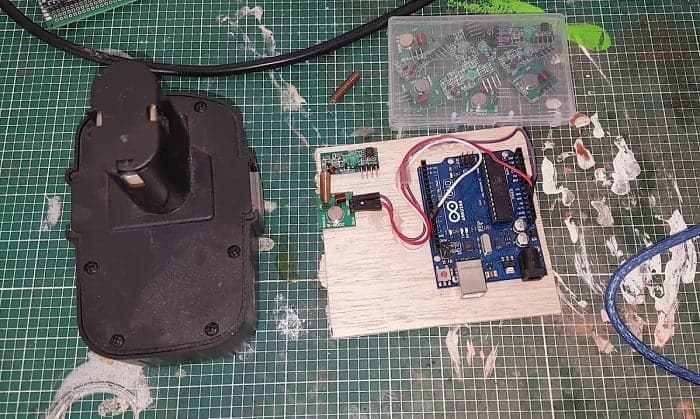
In a normal attack, the disruptions will cause the SmartHome system to become unusable until the attack stops. In more serious cases, a jamming attack can lead to faster discharge of the smart system's battery or even malfunctioning from potential glitches, caused by the attack.
Eavesdropping Attacks
Smart gadgets work by constant communication using Wi-Fi or Bluetooth, making them vulnerable to attacks that can access the exchanged data. This attack type is known as "eavesdropping". This attack also involves stealing valuable/sensitive information shared via the gadgets connected by IoT. This information can later be used in spoofing attacks. After hacking the wireless channel, the adversary can analyze the traffic semantics, employ reverse-engineering, and so on. The main source of an eavesdropping threat comes from the correlation between daily human activities and requests that IoT devices execute.
Over-Privileged Attacks
A common problem of the SmartHome systems is that they have to support numerous third-party apps and gadgets. These apps access the working logic of a smart home, to execute a various command, like "locking the door", "changing the lighting" or "cleaning the room" etc. This access control leads to an issue of imperfect authorization which can grant access to privileges that are not required for an app to execute its primary functions. Typically, when an app requires only limited access to device controls, it will gain access to all or most functions. This may lead to the potential abuse of these privileges. As illustrated by the facial antispoofing Wiki, if an app employs low security measures and is vulnerable, adversaries can hack it to exploit the "privileged access" for various purposes.
Unauthorized Access
As the cases of Owlet and Jeep show, hackers can hijack a smart device. And sometimes, it can be done relatively easily. SmartHome devices can sometimes have a poor authentication algorithms. This is especially true for the Bluetooth devices like smartwatches. A default link key for network joining can also be used to take control of a smart gizmo — this is a relatively easy task for an adversary.
Attacking smart home gadgets over the internet is another tactic. As Wikileaks reports, certain smart TVs can be put in the "listening mode". In this instance, CIA proved to be the main culprit accessing user data. This highlights a certain attack possibility linked to smart devices.
Voice Spoofing Attacks
Voice spoofing attacks, already described by the facial anti spoofing Wiki, use replay attacks to exploit the Voice User Interface (VUI) of a smart system. Adversaries can access the smart system using a recorded voice sample of the actual owner, artificially synthesized voice, or even a hidden voice command — an inaudible request that can be heard by the smart system only.
Mitigating IoT Spoofing Attacks
A number of countermeasures against IoT attacks have been devised. Our facial antispoofing Wiki describes the following strategies:
Anti-Jamming
A jamming attack can be used against a SmartHome system using an external jamming device, or by turning one of the connected smart devices into a jammer. Anti-spoofing for IoT suggests that in the first case, the SmartHome system can mitigate/stop the attack by switching to another frequency channel. In the second case, a special inference framework can be used to detect the source of disturbances and appropriate action can then be taken to stop the attack.
Encryption
Encryption is a classic method used to protect the traffic going in and out of a SmartHome system. Consequently, attackers can be stopped from gaining access to this information. Currently, the 128-bit AES-CCM authenticated encryption algorithm is widely used to protect the network layer. The so-called "dummy traffic" can be used as a decoy to "fool" the analysis based on machine learning.
Anti-privilege
A possible method to prevent spoofing through over-privileged issue is employing the context-based permission system. This system delivers contextual integrity, which, in turn, prevents sensitive actions from being abused, using fine-grained context identification.
Restricting Unauthorized Gadget Access
Preventing unauthorized gadget access can be solved in two ways. First, authentication can be reinforced with the cryptographic "handshake" that happens between smart gizmos via Bluetooth .
The second method involves authentication and a capability-based access control model. This method is often used to ensure a strong gadget-level verification.
Voice Anti-spoofing
Voice anti-spoofing can be carried out using a number of techniques depending on the type of gadget under attack. For wearable gadgets, the acceleration method is commonly used. The method implies that when an actual owner is speaking, certain parts of their skin begin vibrating. Detecting this vibration can help filer out a pre-recorded/synthetic vocal request. (Consult facial anti-spoofing Wiki for more info on voice antispoofing).
An alternative method is based on two-factor authentication. It implies monitoring the lip movement of a speaker by analyzing the channel state information (CSI), which is based on a device-free sensing method.
The procedure involves 4 steps:
- Collecting voice samples & CSI data.
- Noise removal and syllable segmenting in the CSI data.
- Selecting appropriate features from various levels.
- Acceptance/denial of a voice command.
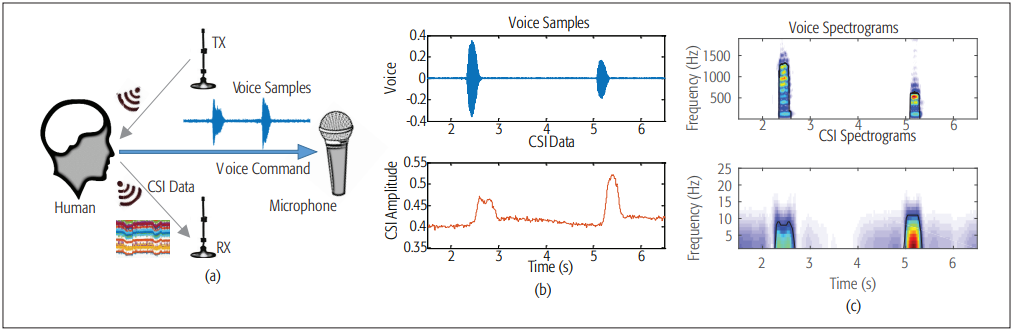
To ensure the accuracy and ampleness of the CSI data, the method uses two antennas connected to various smart gadgets inside the house. An authentic user issued command will reach both antennas and the CSI contours and vocal samples will match. However, a verbal attack will not lead to a match and can therefore, be detected.
References
- History of the Internet of Things (IoT)
- Kevin Ashton — a pioneer RFID researcher
- The research, The Internet of Things: Consumer, Industrial & Public Services 2020-2024, By Juniper Research
- Bluetooth spoofing
- BLE Spoofing Attacks flaw
- Owlet Wi-Fi heart monitors proved to be hackable
- Hackers Remotely Hijacked A Jeep On The Highway
- Researchers highlight 5 attack types that target IoT systems
- How to Make a Radio Frequency Jammer – Detailed Instructions
- Securing Consumer IoT in the Smart Home: Architecture, Challenges, and Countermeasures
- Hidden Voice Commands
- Anti-jamming. A special inference framework
- ContexIoT: Towards Providing Contextual Integrity to Appified IoT Platforms
- MASHaBLE: mobile applications of secret handshakes over bluetooth LE
- Effective Defense Schemes for Phishing Attacks on Mobile Computing Platforms

 Antispoofing
Antispoofing


